Data Interception and Encryption
Sending messages
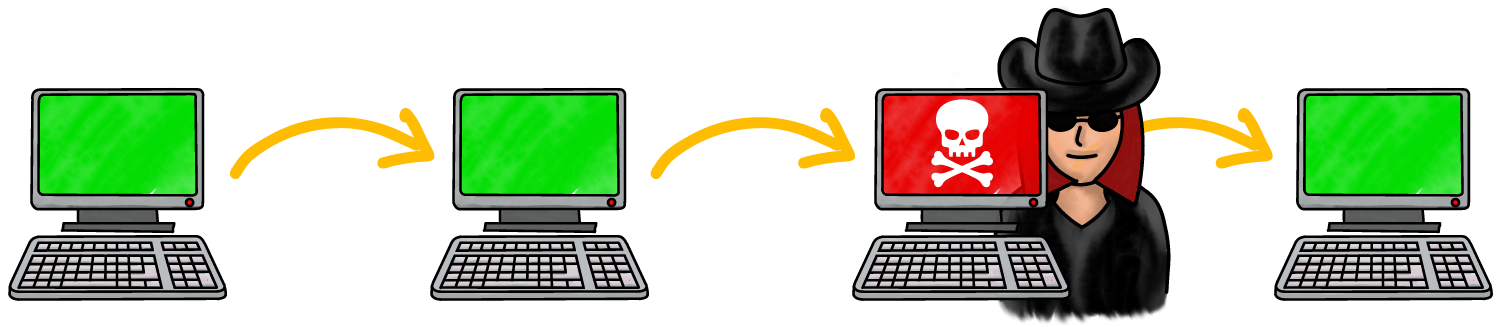
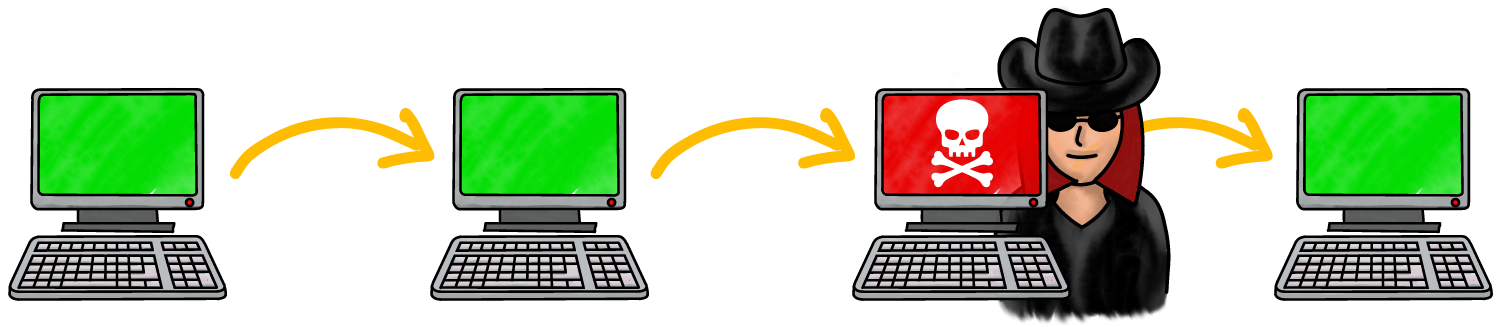
- On a network, like the Internet, computers are connected to other computers
- When sending a message across a network, it might "hop" through several different devices to get to the recipient
- Data interception is when someone copies or changes the data as it hops between devices
- This is often known as a man-in-the-middle attack
- The recipient may not even know the data has been copied or altered

Encryption
- Messages are scrambled, so only the person it's intended for can understand it
- A key is the secret code used to encrypt the data
- Only someone with the correct key can decrypt the data, converting it back to the original message
- If anyone intercepts the data, it will look like nonsense, and they won’t understand it
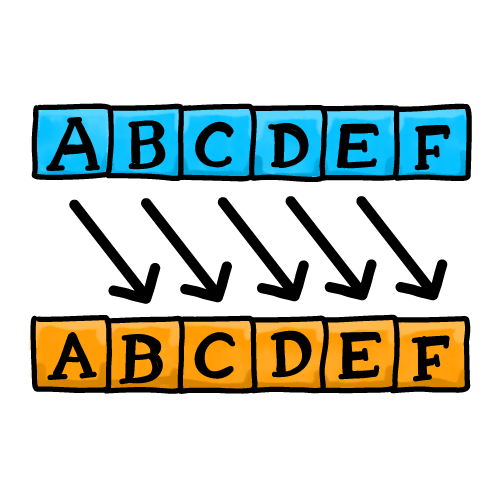
Shift cipher
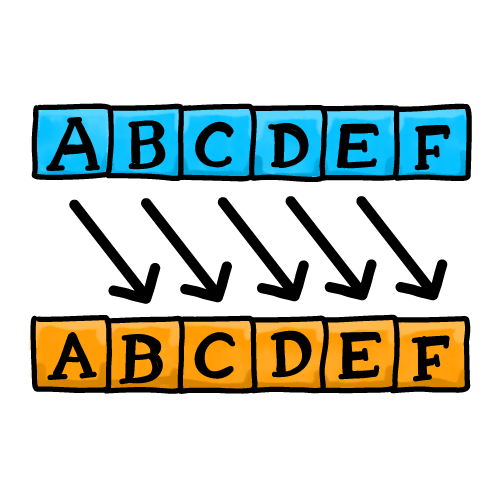
- A shift cipher, or Caesar Cipher, is a very simple way to encrypt data
- Each character is shifted by a number of places (the key)
- To decrypt the message, each character of the encrypted message is shifted back by the same number of places
- In the diagram, the key is 1. Each character is shifted one place, so A becomes B, B becomes C, and so on…
- You can try it yourself by clicking here.
Quick Quiz